Description
Ektron's Solr implementation is subject to the vulnerability documented by CVE-2021-44228.
Ektron Solr versions affected: 9.3SP2 - 9.4SP1
There are no required actions for versions prior to 9.3SP2 as these use an earlier version of Log4j not within the scope of CVE-2021-44228. JMSAppender is also vulnerable but is not used in Ektron's implementation by default.
Log4j release notes: https://logging.apache.org/log4j/2.x/security.html
Steps
Note: Option #1 is recommended to address other log4j vulnerabilities.
Option #1 : Update to Ektron's 9.5 Solr version
For versions 9.3SP2 - 9.4SP1
- Uninstall the existing Solr version
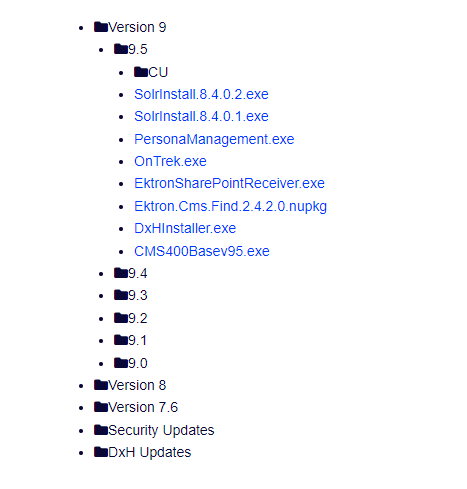
- Download and install 8.4.0.2 Solr executable for 9.5 from the downloads page.
Option #2: Update log4j jar files
For versions 9.3SP2 - 9.4SP1
- Backup the Solr directories.
- Download the latest binary version of log4j (Apache Log4j 2 binary (zip)): https://logging.apache.org/log4j/2.x/download.html
- Delete all log4j jar files within the "\Solr\server\lib\ext" and "\Solr\contrib\prometheus-exporter\lib" directories and replace with the new files in following folders.
Replace X with the sub version of log4j2. E.g. log4j-1.2-api-2.X.jar
\Solr\server\lib\extNew files:log4j-1.2-api-2.X.jarlog4j-api-2.X.jarlog4j-core-2.X.jarlog4j-slf4j-impl-2.X.jarlog4j-web-2.X.jar\Solr\contrib\prometheus-exporter\libNew files:log4j-api-2.X.jarlog4j-core-2.X.jarlog4j-slf4j-impl-2.X.jar
If you would like to verify the log4j version do the below. Log4j versions prior to 2.0 are not vulnerable to CVE-2021-44228.
- In file explorer navigate to the SearchX.0 folder.
- Search for log4j .jar
- Copy those jars to a separate folder.
- Extract the .jar files.
- For each of the "META-INF" folder & open the file "MANIFEST.MF" in a text editor.
- Look for "Implementation-Version" and identify the log4j version.
- In some cases(9.2+) there can be a separate Solr directory, sometimes outside of the SearchX.0 folder. Repeat the above steps for such directories.
Please sign in to leave a comment.